Stop Today’s Hackers – What MHEDA Members Need to Know
May 10, 2022Duration: 57:04
Membership is required to view this video
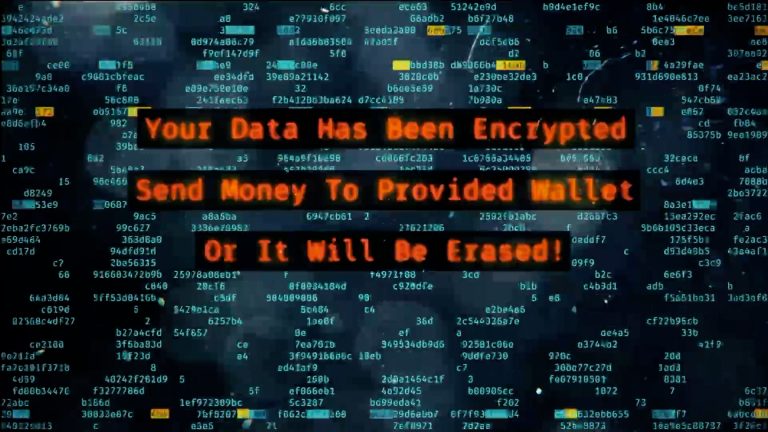
This wasn’t the typical cybersecurity presentation at the 2022 MHEDA annual convention. Mike has an uncanny ability to transform complex computer topics into something easy for everyone to understand which earns him a stellar reputation among clients and colleagues as a go-to IT cybersecurity resource. He’s given more than 1500 keynotes and presentations and knows how to provide valuable information to executives of all levels of experience. Members will leave with concrete action items to make sure their IT professionals, be they in-house or outsourced, are taking the right steps to protect the IT systems. Each year more than 16,000 cyber security attacks take place that results in a quantifiable data breach. Don’t let your company be next.
Takeaways:
- Gain specific guidelines to give to their IT pros;
- Help your company protect against ransomware;
- Ensure a mature incident response plan and disaster recovery plan;
- Address cybersecurity to protect the sensitive data entrusted to their company;
- Be part of the decision-making process by knowing what to ask and how to ask;
- Know how to communicate with your IT team in simple, non-technical language.
About the Speaker
 Mike Foster, CEH*, CISA*, CISSP* is the founder and CEO of Foster Institute. More than 20 years ago he began training people to be more productive in their use of technology. He is a technology expert, author and professional speaker with more than 1,000 presentations under his belt. Mike is author of The Secure CEO: How to Protect Your Computer Systems, Your Company, and Your Job and is regularly sought for interviews and business publication features. He’s been interviewed by USA Today, Forbes Magazine, and The New York Times, as well as many others. Mike explains the most technical, in a common sense “plain English” way that even “low tech” people enjoy. Because Mike’s delivery is down-to-earth, the technical is easy to understand. Mike Foster has a wide range of high-level technology certifications; he also quickly engages even your most sophisticated tech people. *CEH: Certified Ethical Hacker; *CISA: Certified Information Systems Auditor; *CISSP: Certified Information Systems Security Professional
Mike Foster, CEH*, CISA*, CISSP* is the founder and CEO of Foster Institute. More than 20 years ago he began training people to be more productive in their use of technology. He is a technology expert, author and professional speaker with more than 1,000 presentations under his belt. Mike is author of The Secure CEO: How to Protect Your Computer Systems, Your Company, and Your Job and is regularly sought for interviews and business publication features. He’s been interviewed by USA Today, Forbes Magazine, and The New York Times, as well as many others. Mike explains the most technical, in a common sense “plain English” way that even “low tech” people enjoy. Because Mike’s delivery is down-to-earth, the technical is easy to understand. Mike Foster has a wide range of high-level technology certifications; he also quickly engages even your most sophisticated tech people. *CEH: Certified Ethical Hacker; *CISA: Certified Information Systems Auditor; *CISSP: Certified Information Systems Security Professional